Stop data breaches automatically.
- Cloud-native
- Automated
- Battle-tested
Optional Eyebrow
PROTECT YOUR DATA ,
WHEREVER IT LIVES.
Automatically find your critical data, remediate risk, and stop threats – before your data can be compromised.
- dgfdsg
- sdg
- sdgsd
- gdgdtg
Varonis Interceptor
Protect against sophisticated phishing and social engineering attacks with AI-native email security and the best detection rate on the planet.
- 99.9% accuracy
- Deploys in minutes
- API-based
Trusted By Thousands of Companies
Partner with a leader in data security.

ai-powered
End-to-end coverage across the AI lifecycle.
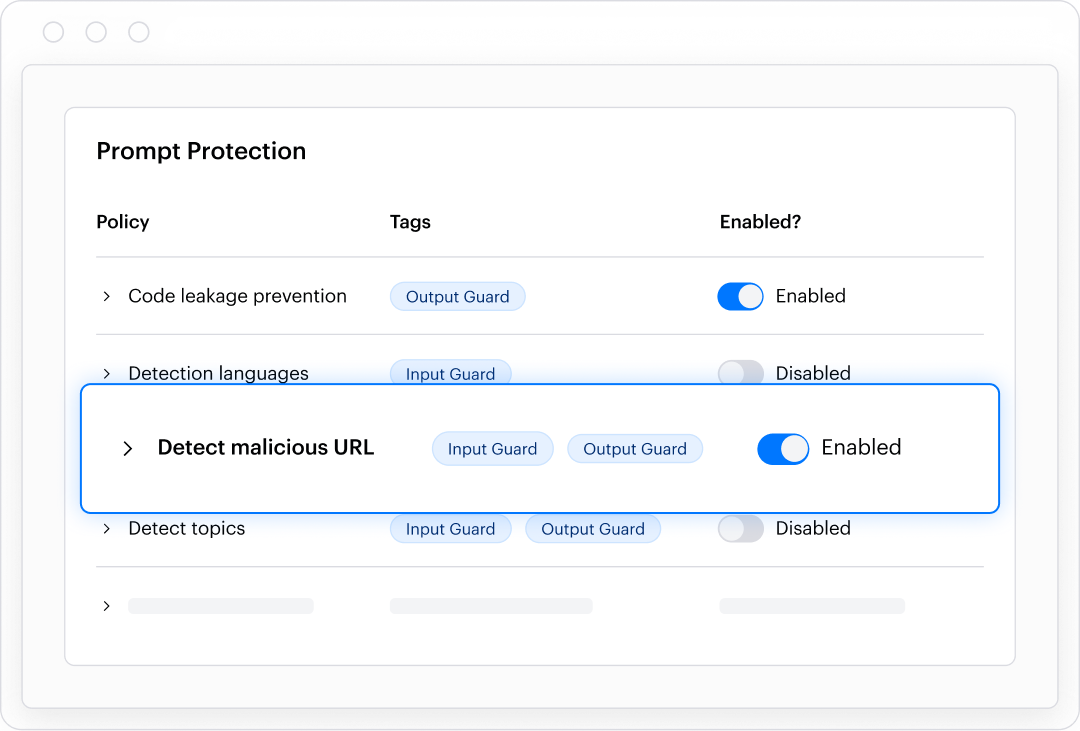
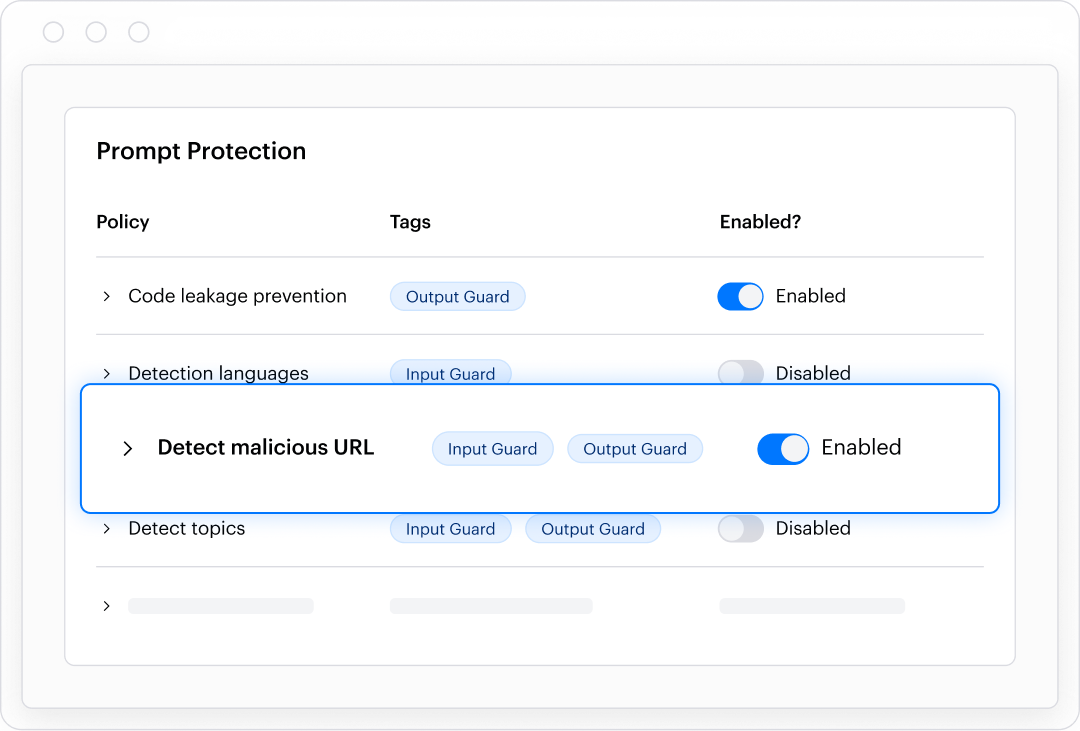
Enforce real-time policies that prevent sensitive data leakage and block malicious and non-compliant use of any AI asset.
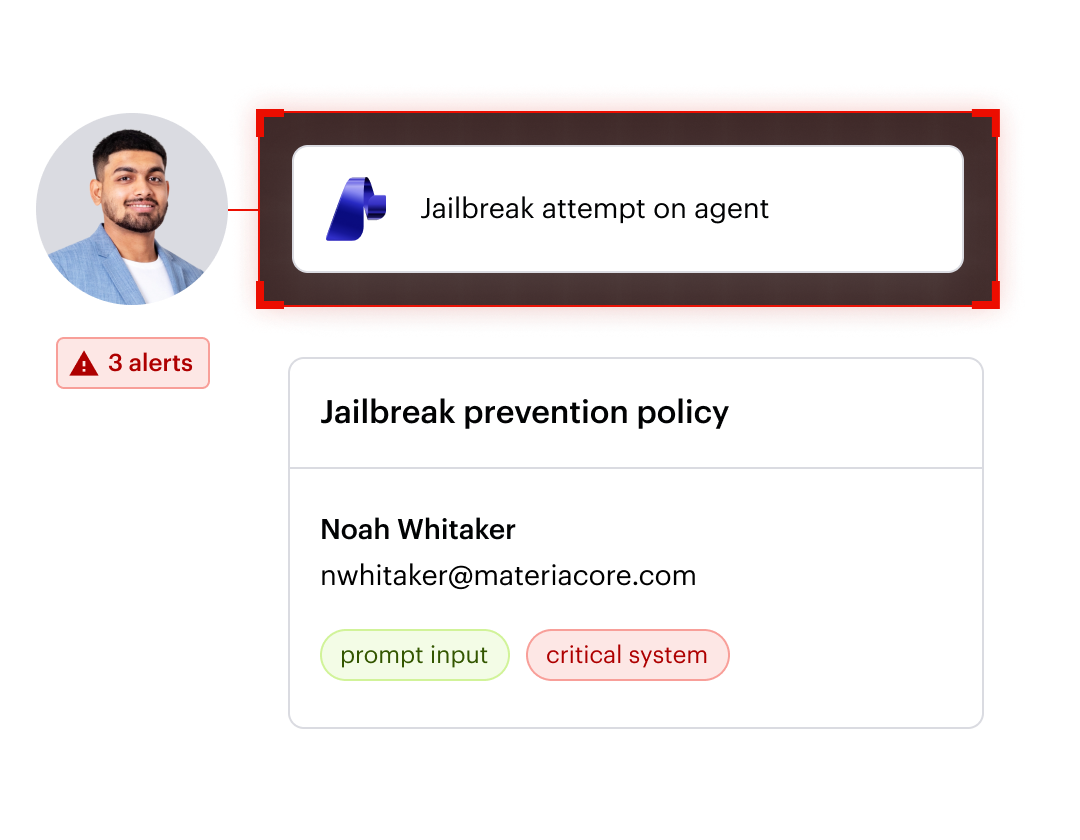
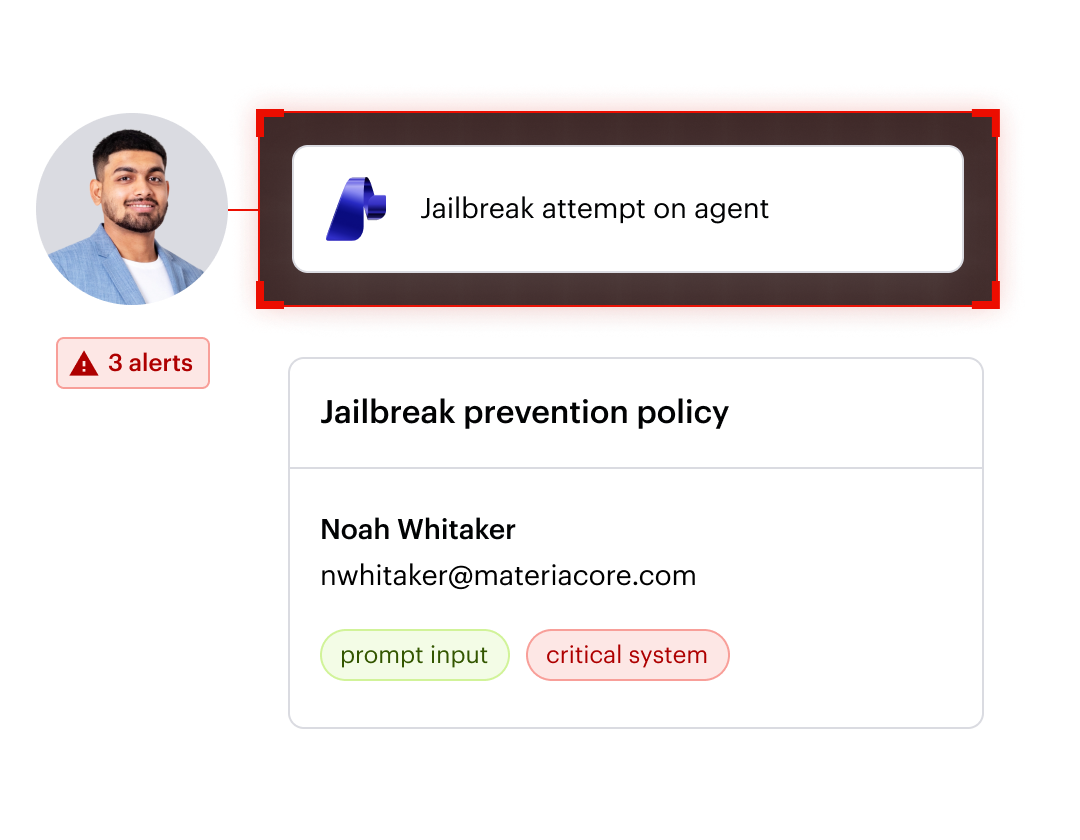
Detect and monitor all AI usage within your organization, store audit events, and generate real time alerts on suspicious or risky behavior.
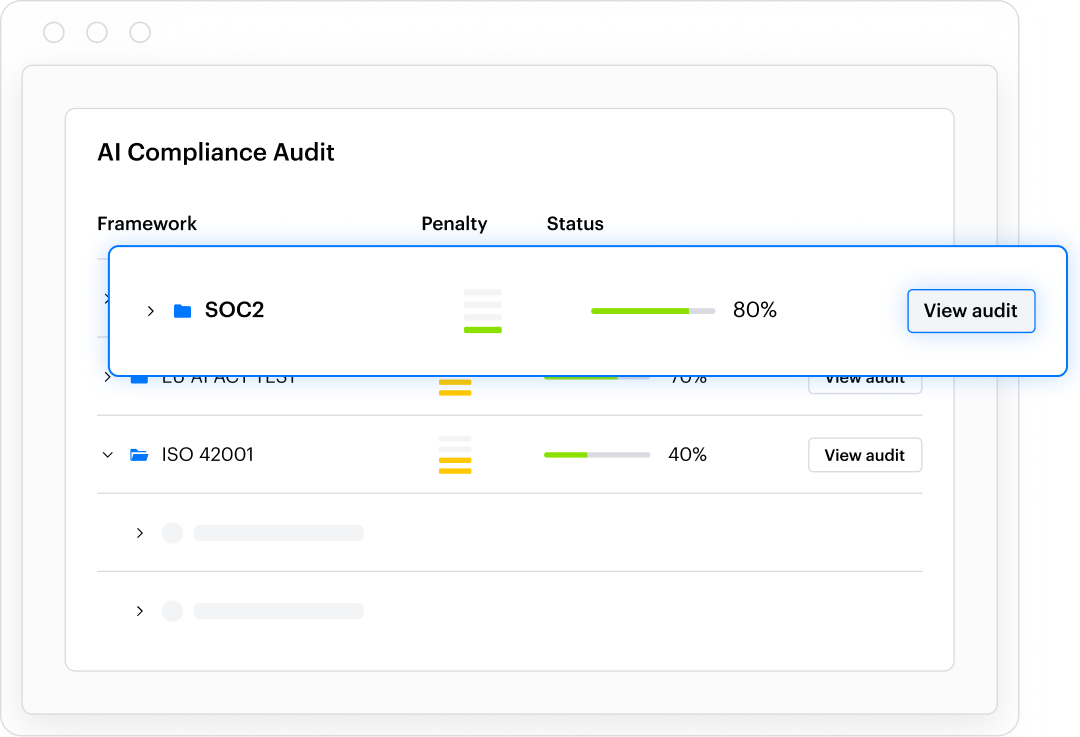
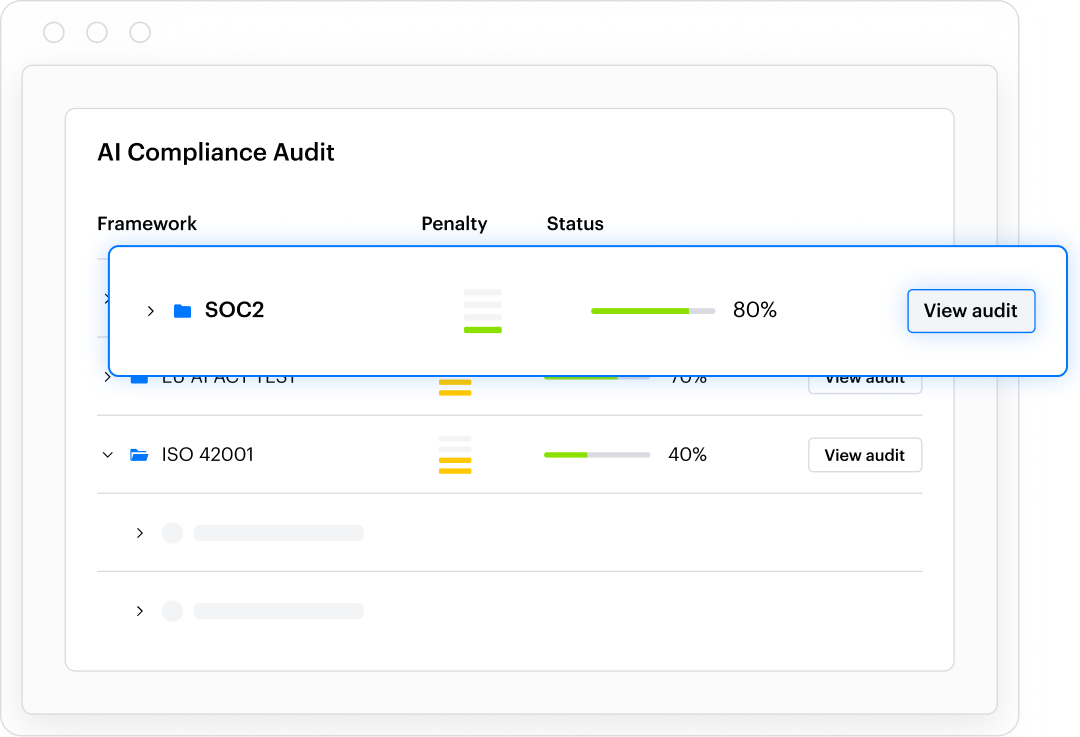
Get out-of-the-box audit reporting to validate your compliance with ever-changing AI regulations and frameworks.
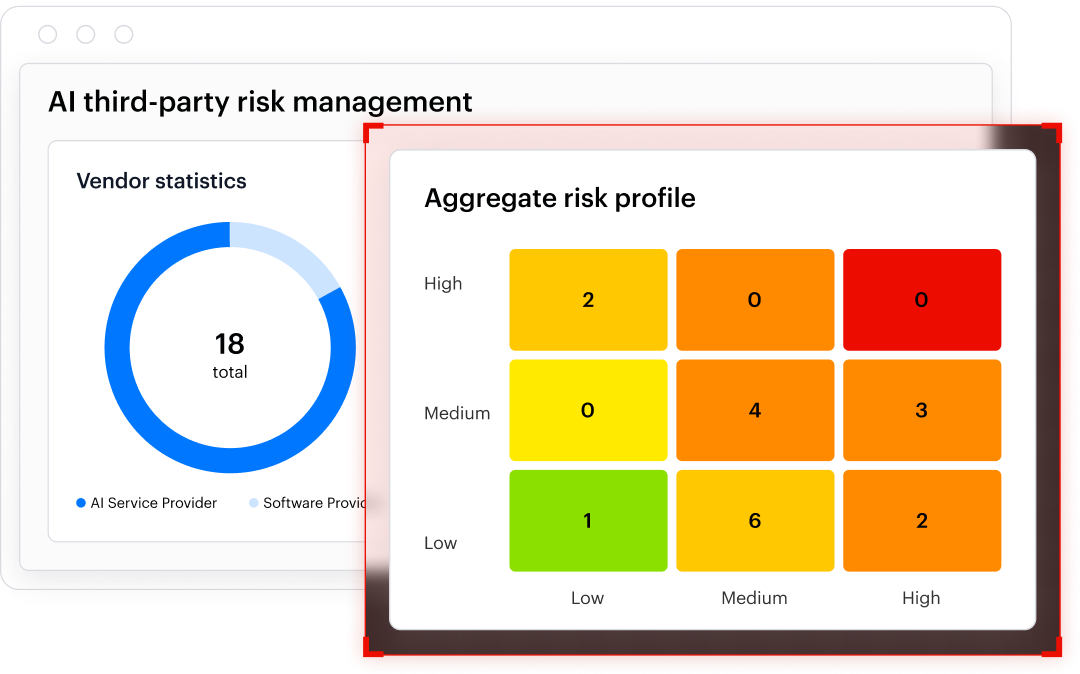
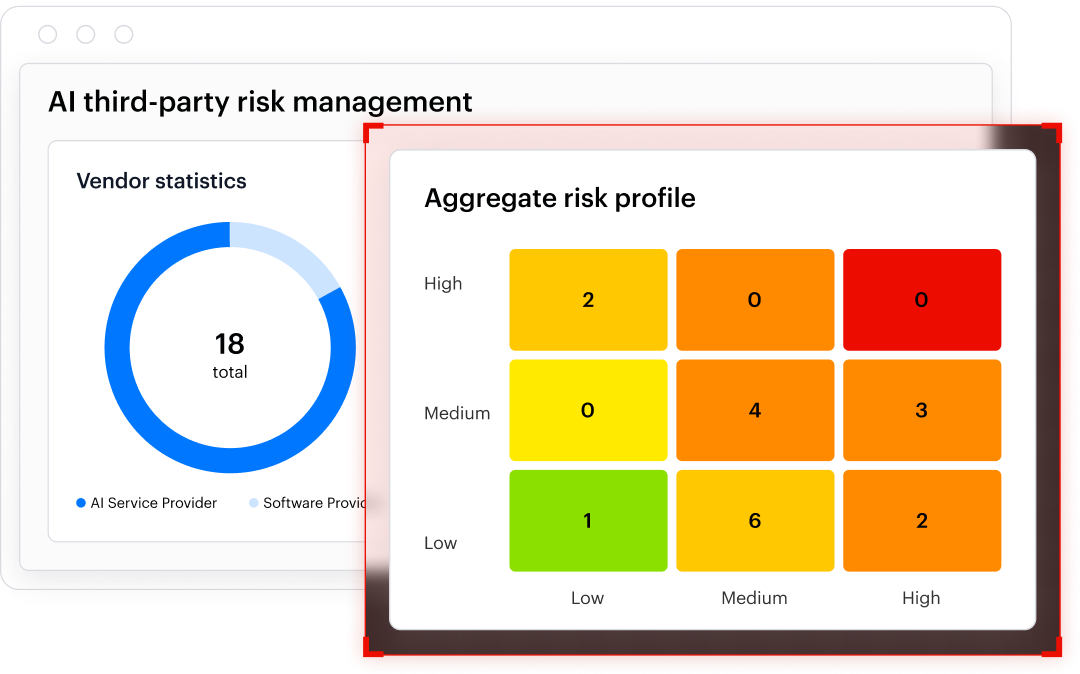
Manage AI use within products and services that you consume through your supply chain and take control of third-party risk.
Enforce real-time policies that prevent sensitive data leakage and block malicious and non-compliant use of any AI asset.
Detect and monitor all AI usage within your organization, store audit events, and generate real time alerts on suspicious or risky behavior.
Get out-of-the-box audit reporting to validate your compliance with ever-changing AI regulations and frameworks.
Manage AI use within products and services that you consume through your supply chain and take control of third-party risk.
overline
BigID only finds data. Varonis protects it.
Test Title

Title no button
Discovery & classification
Periodic, scan-based discovery that can becomes incomplete or stale
Continuous, real-time discovery and classification across large, dynamic environments
Classification depth & context
Classification focused on content and metadata, with limited security context
High-precision classification enriched with identity, permissions, usage, and exposure context
AI security
Offers just inventory and governance; lacks active blocking or remediation
Full-stack AI security via AllTrue acquisition: red teaming, AI-SPM, observability, runtime protection, and compliance
Threat detection & response
No threat detection or real-time monitoring of data access
Behavior-based threat detection (UEBA) for insider threats, compromised identities, ransomware, and data exfiltration
Identity & behavior analytics
No identity-driven or behavior-based analytics
Native correlation of users, service accounts, roles, and behavior to sensitive data
Automation & remediation
Title
Limited automation via manual workflows and ticketing systems—requires human intervention to fix risks
Built-in, automated remediation to reduce exposure, enforce least privilege, and lock down data at scale
Expert Services
No IR offering. Dedicated support and “BigID Concierge” are paid, add on licenses
Offers expert 24/7 MDDR with SLA. Varonis Concierge post-sale services are included at no extra cost
Pricing Module
Variable pricing based on data volume and scan depth, with core security outcomes like permission management, remediation, and privacy are sold as separate add-ons
Single platform price includes classification, permissions management, threat detection, remediation, and expert services
Protect
Ready to see the #1 Data Security Platform in action?
Why? Cybersecurity didn’t start with data. It started at the borders, where attackers should be held at bay, far from precious data at the heart of the kingdom.
The security perimeter has vanished. Endpoints are fungible. Very little data lives only on your phone or laptop these days.
At Varonis, we protect data where it lives. Our platform is purpose-built to look deeply inside and around data—and then automate its protection using patented, battle-hardened machine learning.


